AI-Powered Research Intelligence for Scholars
Analyze research papers, reports, datasets, and literature faster with clarity, structure, and precision. Transform information overload into actionable insight.
Compliance requires precision — but documentation creates complexity
Manually reviewing, cross-checking, and tracking obligations across these documents is time-consuming and increases the risk of oversight. When regulations evolve, the pressure to stay aligned becomes even greater.
- Regulatory Guidelines
- Internal Policies & SOPs
- Vendor Agreements
- Risk Assessment Reports
- Audit Documentation
- Compliance Checklists
Precision at Every Step
Five core capabilities designed to reduce manual effort, minimize risk exposure, and keep compliance teams ahead of regulatory change.
01
Intelligent Document Querying
Ask compliance-specific questions and receive context-aware responses sourced directly from your uploaded documents, with full traceability.
02
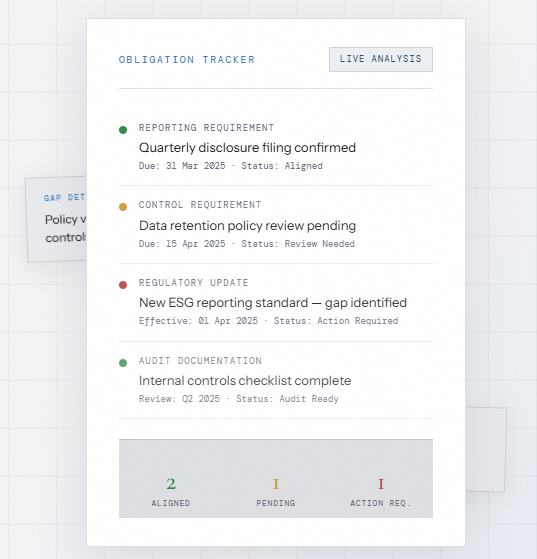
Obligation & Control Extraction
Automatically identify reporting requirements, deadlines, regulatory duties, and internal controls embedded in complex documentation.
03
Policy vs. Regulation Comparison
Compare company policies with external regulatory frameworks to detect gaps, conflicts, or missing controls before they become risks.
04
Structured Compliance Summaries
Generate clear summaries highlighting key obligations, risks, and action items — formatted for immediate team use or audit presentation.
05
Secure Document Processing
Maintain full control over sensitive compliance data with protected and controlled document handling at every stage of your workflow.
↓60%
Manual Review Time
100%
Document Traceability
Multi
Framework Support
Zero
Data Exposure Risk
Where Teams Use ZDS
Compliance Applications
- Regulatory compliance monitoring
- Internal audits and risk reviews
- Vendor compliance assessments
- Policy alignment checks
- ESG and governance documentation
- Preparing for regulatory inspections
- Documentation review during M&A
Real Compliance Benefits
- Reduce Manual Document Review Time
- Improve Visibility into Obligations
- Strengthen Audit Readiness
- Enable Faster, Data-Backed Decisions
Enterprise Ready
White Label
ZDS can be tailored for organizations of every type and scale, with white-label and private deployment options available.
- Corporate Compliance Departments
- Risk Management Teams
- Regulatory Consulting Firms
- Financial Institutions
- Governance & Internal Control Teams


Data Protection
Security You Can Trust
Compliance data is highly sensitive and often confidential. ZDS is designed with security at its core.
Security Protocols
- Controlled document access & permissions
- Secure processing environments
- Strict confidentiality protocols
- Optional customised or private deployments
- Regulatory & audit documentation protected at every stage
