Turn Complex Client Documents into Clear, Actionable Insights
Faster, smarter, and with complete confidence — built for the pace of high-performance consulting.
Consulting moves fast — but documents slow teams down
Manually reviewing and extracting insights from large volumes of documents consumes billable hours and delays client delivery.
- Client contracts & agreements
- Financial reports & performance data
- Due diligence documentation
- Regulatory & compliance materials
- Strategy decks & research reports
- Internal knowledge archives
Five Core Capabilities
Precision tools designed for the demands of consulting — from client briefings and due diligence to M&A documentation and regulatory advisory.
01
Intelligent Document Querying
Ask precise business or compliance questions and receive answers directly sourced from uploaded documents — with full traceability.
02
Structured Executive Summaries
Generate concise summaries ideal for leadership briefings and client presentations — ready to use, formatted for decision-makers.
03
Multi-Document Analysis
Compare financial reports, contracts, and strategic documents to identify trends, gaps, and inconsistencies across any engagement.
04
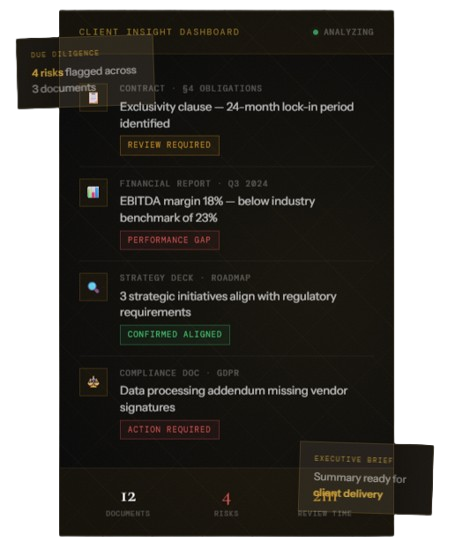
Risk & Insight Extraction
Automatically identify critical clauses, performance indicators, obligations, and potential risk areas within complex client documentation.
05
Secure Client Data Handling
Maintain confidentiality with controlled access and secure document processing — built for the sensitivity of consulting engagements.
↓70%
Non-Billable Review
2×
Faster Client Delivery
Multi
Document Comparison
100%
Client Confidentiality
Where Consulting Firms Use ZDS
Consulting Applications
- Due diligence and transaction advisory
- Strategy consulting projects
- Operational performance analysis
- Regulatory and compliance consulting
- Mergers & acquisitions documentation review
- Internal knowledge management
- Client audit preparation
Real Consulting Benefits
- Reduce Non-Billable Review Time
- Deliver Faster Client Insights
- Strengthen Risk Assessment Capabilities
- Increase Competitive Advantage
Scalable Deployment
White-label for Consulting Organizations
ZDS can be deployed as a tailored solution — fitting seamlessly into your firm’s existing workflow and brand.
- A firm-wide document intelligence platform
- A private internal knowledge system
- A white-label solution under your consulting brand


Client Confidentiality
Confidentiality Comes First
Consulting engagements often involve highly sensitive client data. ZDS is built with confidentiality as a core requirement — not an afterthought.
Security Protocols
- Controlled document access & permissions
- Secure processing environments
- Strict confidentiality protocols
- Optional private or dedicated deployments
