AI-Powered Document Intelligence for Software Companies
Transform technical documentation, contracts, and compliance files into structured, actionable insights — instantly.
Software teams move fast — but documentation slows them down
As companies scale, managing and extracting insights from documentation becomes increasingly complex. Manual review processes slow down product releases, compliance audits, and strategic decisions.
- Tech Specs
- PRDs
- API Docs
- Security Policies
- SLAs & Contracts
- Knowledge Bases
- Vendor Agreements
Five Core Capabilities
Five core capabilities designed to reduce manual effort, minimize risk exposure, and keep compliance teams ahead of regulatory change.Purpose-built to handle the speed and complexity of software documentation — from PRDs to vendor SLAs to compliance audits.
01
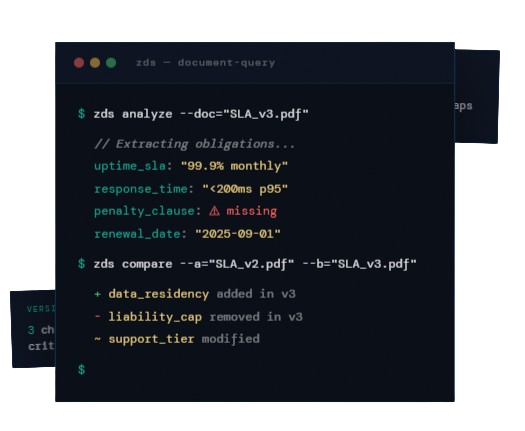
Intelligent Document Querying
Ask technical or compliance-related questions and receive accurate, context-aware responses sourced directly from your documents.
02
Requirement & Clause Extraction
Automatically identify functional requirements, SLAs, performance benchmarks, and contractual obligations across any document.
03
Multi-Document & Version Comparison
Compare documentation versions to detect changes, missing requirements, or inconsistencies — across specs, policies, or contracts.
04
Structured Technical Summaries
Generate concise summaries ideal for engineering reviews, leadership updates, or investor reporting — formatted for immediate use.
05
Secure Document Processing
Maintain strict control over proprietary code documentation, internal policies, and client agreements at every stage.
↓65%
Doc Review Time
∞
Version Comparisons
100%
Source Traceability
Zero
IP Exposure Risk
Where Software Companies Use ZDS
Technical Applications
- Product requirement analysis
- Contract & SLA review
- Security & compliance documentation checks
- Vendor risk assessments
- Audit preparation
- Knowledge base consolidation
- Due diligence for funding or acquisition
Real Engineering Benefits
- Accelerate Documentation Review
- Reduce Compliance & Contractual Risk
- Improve Cross-Team Visibility
- Support Faster, Data-Backed Decisions
white-label system
Built for Organizations
Designed to scale with startups, mid-sized tech firms, and enterprise software companies.
- An internal document intelligence platform
- A compliance monitoring tool
- A secure knowledge management system
- A white-label solution for SaaS providers


Intellectual Property Protection
Protect Your IP
Software companies handle highly sensitive materials. ZDS is engineered to keep them secure.
Security Protocols
- Controlled document access & permissions
- Secure processing environments
- Confidential data handling
- Optional private deployments
- IP protected at every stage
